Dispersive® Stealth Networking

You Can't Attack
What You Can't See
Dispersive® Stealth Networking delivers quantum-resilient secure networking that makes enterprise communications and data-in-motion invisible and shielded by design. Gain sovereign control of critical systems, enclaves, AI workloads, and distributed operations.
Remove the Visibility Attackers Need to Target You
Eliminates exposed paths and patterns, making your network extremely difficult to find, map, or exploit — even with AI driven reconnaissance.
Protect Data in Motion, Regardless of the Network
Keeps communications hidden and intact across paths you don't own or control. Attackers cannot intercept, observe, or correlate traffic in motion, even when they're on the same infrastructure.
Ensure Continuous, Resilient Performance Under Any Conditions
Delivers stable, high performance connectivity across cloud, hybrid, and edge environments — with no failover events, no performance collapse, and no operational downtime.
The Network Layer No One Secured, Until Now
Every major security investment of the last decade strengthened access control, identity, and application protection. Each layer assumes one thing: that the network beneath it is safe. It is not.
Data in motion still exposes paths, patterns, and behaviors that can be observed, mapped, and exploited, even when encrypted. Dispersive® Stealth Networking operates at the layer all other tools assume but leave unprotected. It fragments data across dynamic, non-deterministic paths, making traffic invisible and communications resilient by design. No single stream exists to intercept. No predictable route exists to target.
Others assume the network can be trusted.
Dispersive® Stealth Networking operates when it's not.
AI Infrastructure Runs on an Unprotected Layer
AI systems are now infrastructure. The communications fabric connecting models, GPUs, and orchestration layers moves continuously, across cloud, edge, and public internet, and almost none of it is protected at the transport layer. Current security tools govern access to AI systems. They do not control how the traffic between them behaves, who can observe it, or what it reveals.
Encryption addresses part of this. It does not address all of it. Large language models stream responses token-by-token, producing a timing pattern that functions as a fingerprint for conversation topics, without exposing the content itself. Independent testing confirmed this class of attack identifies sensitive topics with over 98% accuracy, passively, leaving no forensic evidence. What's inside the packet stays hidden. What the packet reveals about intent does not.
Dispersive® Stealth Networking eliminates the pattern, not just the content. Traffic is fragmented across dynamic, non-deterministic paths so no single observer can capture a complete stream or extract a signal from it. The same architecture that protects AI workloads protects every other communication moving across infrastructure you don't own or control.
Architect the Transport Layer AI Workloads Demand
See how Dispersive® Stealth Networking makes data in motion invisible to adversaries and resilient under attack, without changing your network or your existing security stack.
How Dispersive® Stealth Networking Works
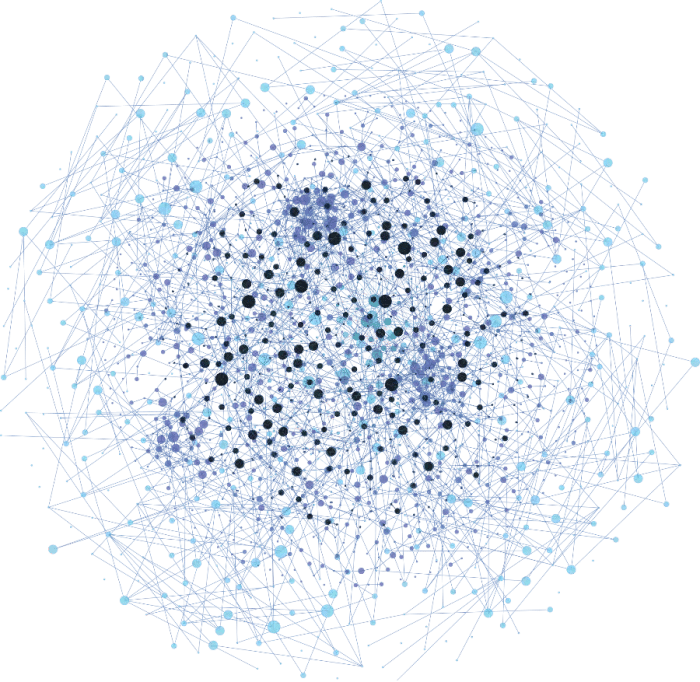
Dispersive® Stealth Networking hides data-in-motion by splitting, encrypting, and obfuscating traffic across multiple diverse network paths simultaneously. Unlike traditional VPNs, SD-WAN, SASE, or Zero Trust overlays, Dispersive eliminates exposed tunnels and predictable routes, thereby removing the attack surface rather than trying to defend it.
Multi-path Obfuscation
Dispersive® Stealth Networking breaks traffic into encrypted fragments and sends each piece across multiple channels and constantly shifting pathways. Because no full packet ever travels through a single route, there is nothing meaningful to intercept, correlate, or reconstruct. This defeats reconnaissance, blocks packet capture, and removes observable flow patterns, eliminating the data-in-motion attack surface altogether.
Quantum-Ready Encryption
Each fragment is protected with multi-layered, NSA-level encryption designed for both current and emerging threats. Even if one fragment were captured (which stealth prevents), it would be meaningless on its own and resistant to future quantum decryption. Stealth and encryption work together to ensure nothing valuable can be collected today or broken tomorrow.
Self-Healing Resilience
If a route becomes degraded, jammed, or attacked, Dispersive® Stealth Networking instantly shifts fragments across alternative channels without disrupting sessions or performance. Instead of defending a single path, the network continuously adapts in motion; sustaining uptime and throughput even under active attack, congestion, or infrastructure instability.
Award Winning Innovation
Proven in High Consequence Environments
Dispersive® Stealth Networking is recognized for advancing secure, resilient communications across government, critical infrastructure, and global enterprises. Our patented transport layer architecture has been validated in mission critical deployments where continuity, invisibility, and performance cannot fail.






















Trusted AWS Partner for Secure,
High Performance Workloads
Dispersive® Stealth Networking integrates seamlessly with AWS to provide invisible, resilient transport for sensitive workloads, secure enclaves, OSINT operations, and distributed cloud environments. Whether supporting regulated data, mission critical applications, or cross region architectures, Dispersive delivers a sovereign transport layer that strengthens and extends your AWS deployments.

Dispersive® Stealth Networking Solutions
Fortifying Networks with Secure, Resilient, and High-Performance Connectivity
DispersiveCloud™
DispersiveCloud™ is a hosted SAAS SOC 2 Type II-compliant solution that brings the power of our groundbreaking network fabric that simplifies the deployment and management process without compromising performance or security. We operate on state-of-the-art cloud networks, partnering with various vendors, including Amazon Web Services and Azure to enable global high availability.
DispersiveFabric™
DispersiveFabric™ is our robust, flexible solution designed for larger, more complex environments. A software-defined overlay network, DispersiveFabric™ utilizes a microservices architecture to provide unparalleled security, reliability, and performance. Deployable on any type of infrastructure with infinite scale- public cloud, private cloud, containers, VMs, dedicated hardware.
.jpg?width=912&height=912&name=iStock-1361547059%20(1).jpg)
Others Assume
the Network Can Be Trusted
We'll show you where it isn't. Then we’ll show you exactly what protecting it looks like in your environment.
Stay Ahead with Expert Insights
Stay informed with expert analysis, best practices, and deep dives into the latest cybersecurity challenges and developments to strengthen your security posture.




